As you may or may not be aware, a new GNU bash exploit has been disclosed by the name of ShellShock, (CVE-2014-6271). This affects the VPS hosting clients running Linux.
What can ShellShock be used for?
ShellShock makes your servers vulnerable to remote attacks from attackers without you in the knowledge. The most common attack is attackers writing CGI to remotely perform commands on a vulnerable target.
Am I vulnerable?
You can easily check if you are vulnerable to a attack. To do so, enter the following command in your shell.
env ‘VAR=() ; echo Bash is vulnerable!’ ‘FUNCTION()=() ; echo Bash is vulnerable!’ bash -c “echo Bash Test” .
If the code reports Bash is vulnerable!, you are vulnerable.
How can I protect my Shell?
Luckily, a patch has been released and is avaliable to upgrade. You can upgrade your BASH by following the below commands.
CentOS/Fedora/Redhat
sudo yum update bash -y
Debian/Ubuntu
sudo apt-get update && sudo apt-get install –only-upgrade bash
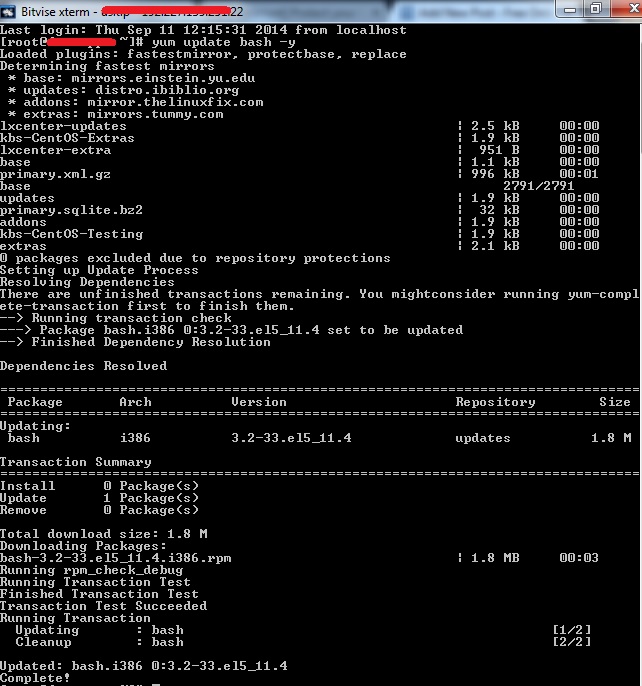
[root@xxx ~]# yum update bash -y
Loaded plugins: fastestmirror, protectbase, replace
Determining fastest mirrors
* base: mirrors.einstein.yu.edu
* updates: distro.ibiblio.org
* addons: mirror.thelinuxfix.com
* extras: mirrors.tummy.com
lxcenter-updates | 2.5 kB 00:00
kbs-CentOS-Extras | 1.9 kB 00:00
lxcenter-extra | 951 B 00:00
base | 1.1 kB 00:00
primary.xml.gz | 996 kB 00:01
base 2791/2791
updates | 1.9 kB 00:00
primary.sqlite.bz2 | 32 kB 00:00
addons | 1.9 kB 00:00
kbs-CentOS-Testing | 1.9 kB 00:00
extras | 2.1 kB 00:00
0 packages excluded due to repository protections
Setting up Update Process
Resolving Dependencies
There are unfinished transactions remaining. You mightconsider running yum-compl
ete-transaction first to finish them.
--> Running transaction check
---> Package bash.i386 0:3.2-33.el5_11.4 set to be updated
--> Finished Dependency Resolution
Dependencies Resolved
================================================================================
Package Arch Version Repository Size
================================================================================
Updating:
bash i386 3.2-33.el5_11.4 updates 1.8 M
Transaction Summary
================================================================================
Install 0 Package(s)
Update 1 Package(s)
Remove 0 Package(s)
Total download size: 1.8 M
Downloading Packages:
bash-3.2-33.el5_11.4.i386.rpm | 1.8 MB 00:03
Running rpm_check_debug
Running Transaction Test
Finished Transaction Test
Transaction Test Succeeded
Running Transaction
Updating : bash [1/2]
Cleanup : bash [2/2]
Updated: bash.i386 0:3.2-33.el5_11.4
Complete!